In this blog, a Fivecast Tradecraft Advisor discusses the threats and challenges associated with a continuously growing online landscape, and how robust intelligence strategies and solutions can mitigate the challenges of identifying threat actors online.
For protective security teams across the government and commercial sector, it’s hard to think of the internet and, more specifically, the advent of social media as anything other than a nightmare. Not only does social media allow organizations and/or protectees to share seemingly innocuous information, pictures, and videos that can help threat actors identify offline patterns of life, the sense of anonymity the internet gives users causes some to make outrageous threats or statements on social media they would never say in person. This includes threats and damaging lies that, no matter their outrageousness, must be fully investigated and sometimes mitigated by team members both online and offline.
READ OUR OSINT FOR PROTECTIVE SECURITY INDUSTRY BRIEF
Identifying Security Threats
Addressing these problems through manual collection and analysis of online content is a huge, unreliable time sink – not least because the sheer volume of content online can make it extremely difficult to separate the signal from the noise, if the noise can even be collected in the first place. It can take so long to identify threats sometimes that analysis isn’t even possible, leading you to a situation where the only response is to increase or change a physical security plan. This is an expensive and time-consuming task at the best of times, and having to do it on the fly only makes matters worse. This cuts across protective security use cases – whether you’re dealing with executive protection, facility, asset, IP, and employee protection, or event security.
Even in situations when the threat is identified with plenty of time to vet it, that process is reminiscent of this famous New Yorker cartoon by Peter Steiner in 1993:
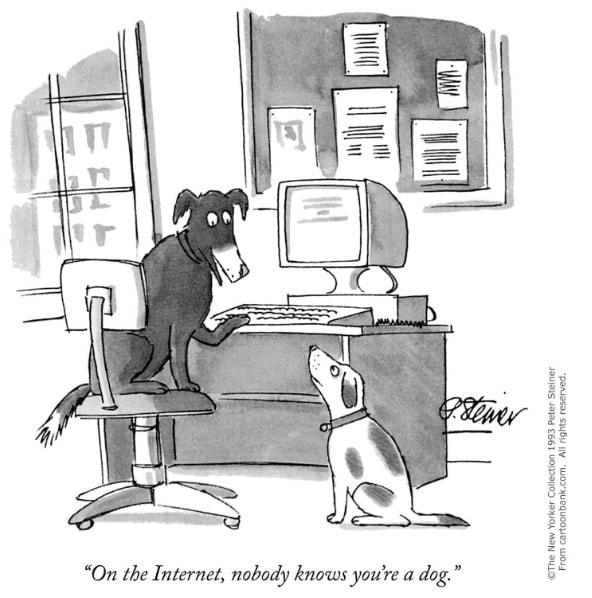
I constantly think of this comic when conducting OSINT analysis – not just because seeing it always makes me laugh – but because one of the most important things a protective security analyst needs to do is determine who is making a threat and use that information to start building out a threat profile. This analysis can and should include a look at the poster’s other activity online, along with a look at any potentially problematic relationships – whether those are with local criminal groups, violent extremists, current and former employees, or any other groups, entities, or individuals that could speak to their intent, capabilities, and access.
This, of course, may sound simple on the surface but it can often be even more time-consuming than the seemingly endless process of manual data collection. This is especially true in cases where the potential threat actor’s identity isn’t immediately obvious, due to a screen name that clearly isn’t the poster’s legal name, strict privacy settings, or conflicting or obviously false information on their page.
Even when the screen name isn’t a legal name, though, an investigator can often learn much from it – whether it’s a nickname, a reference to a person, group, or ideology that someone likes, or even something completely random. A random or obscene screen name, for instance, may not lead an investigator directly to the poster’s identity – but it can be a sign that the poster is security conscious, and created the account with the specific intention of saying things they don’t want traced back to them.
Leveraging OSINT for Protective Security
Despite the challenges of leveraging online content for protective security efforts, the unique information and indicators that threat actors leave behind online offer protective security analysts the opportunity to identify and mitigate threats before they escalate. In order to take advantage of these opportunities, though, protective security teams must overcome major volume challenges. This is where and why many protective security teams have turned to OSINT tools like Fivecast ONYX which mitigates the volume challenge by removing the data collection burden from users, allowing them to focus on using robust, AI-enabled analytical capabilities to sift through masses of potentially relevant data more quickly and efficiently than ever before. This allows analysts to spend more time using their brains and expertise, and less in the boring, rote work of scanning and recording all potential threat comments or content. This, in turn, makes online threat identification and vetting faster, more reliable, and less painful for the analyst team and results in more efficient offline decisions being made about physical investigations and security measures, saving the organization time, money, and effort all while enhancing the security of their executives, facilities, employees, and IP.
To learn more about OSINT for Protective Security Use Cases, request a demo from our experienced Tradecraft team.

