Supporting your mission
Fivecast OSINT solutions are in operational use with law enforcement, defense intelligence, national security, corporate security and financial intelligence customers across the USA, APAC, UK and Europe. With Fivecast, you’ll have unmatched power to drive any investigation forward, shining a light into the darkest of places.
Explore our range of use cases below and then request a customized demo with our intelligence trained Tradecraft team to learn more about how Fivecast can help you find that needle in the haystack to address your biggest intelligence challenges.

The online world fluidly transcends borders making it easier for violent extremist groups and terrorist cells to reach a broader audience, radicalize and incite violence. Fivecast helps law enforcement and counter-terrorism agencies monitor violent extremist movements and better understand their operational capabilities and motivations through advanced capabilities including:
- Automated collection against a wide range of online sources with the ability to track threat actors as they switch online platforms
- AI-enabled risk analytics that can interpret threats appearing in the form of images, videos, written text, or digital network connections
- Graphical analysis of changes in sentiment, emotion, topics and frequency of posts to alert analysts to emerging threats

Learn more about how Fivecast can support counter-terrorism and extremist threat monitoring:
The vast number of security clearances and screening activities required annually by government and the corporate sector coupled with masses of relevant online data can form an almost impenetrable barrier to effective security background investigations. However, as the digital landscape grows, it can also hold the key to more effective, automated and continuous security vetting.
Fivecast is uniquely suited to background security investigations, digital footprinting and continuous evaluation, enabling analysts to perform targeted and entity-centric data collection to:
- Quickly discover and identify account handles relevant to an investigation
- Automatically collect, risk-assess and store a subject’s publicly available social media presence even if accounts or posts are deleted after collection

Learn more about how Fivecast supports security assessments and screening:
Knowing and uncovering the indicators of suspicious activity that may lead to insider threats are critical capabilities for security teams within government agencies, corporations and defense industry primes.
Fivecast facilitates insider threat detection with comprehensive and timely insights into online activities across a broad range of publicly available data, helping to highlight risks that protect companies and communities. Entity-centric data collection and analysis provides analysts with:
- Unprecedented access to information and the ability to ask specific questions of the collected data
- Rapid identification of risk indicators such as unexplained wealth enabled through customizable risk detectors
- Advanced network analysis to explore an relevant connections and associations
Opinions for and against entities and institutions flow freely through social media. However, this dynamic is open to abuse from actors who wish to manipulate such public opinion via online influence operations.
The ability to monitor and assess public attitudes is an operational and strategic necessity. Particularly suited to the nuances of understanding foreign influence, Fivecast helps gain a broad understanding of the issues with:
- Discovery and ongoing data collection to identify specific individuals, groups or movements affecting public opinion or sentiment
- Trend analysis of how online activities related to an issue change over time, highlighting new content, networks and risks
- Configurable risk detectors to rapidly extract relevant topics or issues hidden in multi-media data
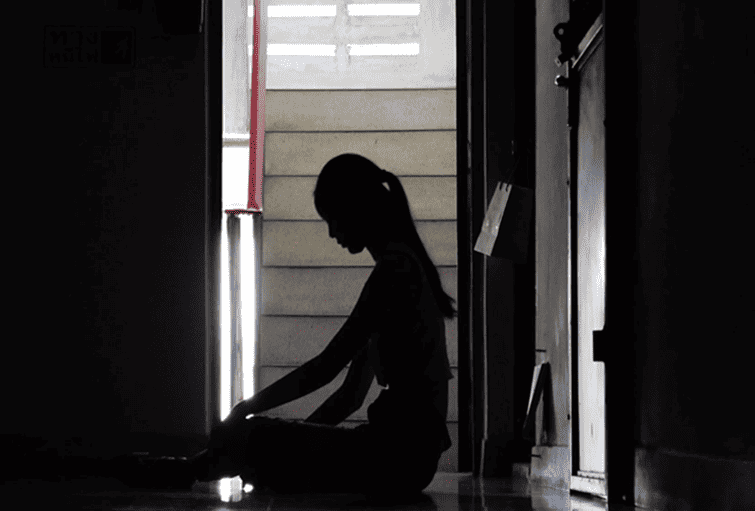
Traffickers are increasingly using online technologies to reach a larger audience, sell illicit goods, develop supply chains and, in cases of human trafficking, groom and traffic victims.
OSINT can be deployed to detect a range of trafficking activities, including; Human, Wildlife & Drug Trafficking, Illegal Trade & Arms Trafficking, Laundering of profits & Illegal Immigration. Fivecast specifically supports these missions by providing a robust OSINT solution which allows intelligence teams to:
- Quickly prioritize likely criminal activity or behavior for analysis with user-configurable risk analytics
- Securely access the broadest Dark Web data set possible with over 750 Dark Web forums & marketplaces via a single search interface
- Rapidly discover individuals, networks, intent & capability
Learn more about how Fivecast can be deployed to monitor trafficking organizations:
Intelligence teams need to anticipate and address potential threats to forces which could impact operations, personnel, assets, critical information and facilities as a result of hostile groups trying to disrupt defense operations.
Publicly available data provides intelligence teams with valuable insight into the networks and capabilities of threat groups. Fivecast enhances traditional intelligence capabilities, providing critical anticipatory threat intelligence and situational awareness through:
- AI-enabled risk detection that delivers critical anticipatory threat intelligence, identifying threats and potential targets
- Automated, continuous and repeatable monitoring of threat groups and their networks
- Customizable logo and image detection that enables intelligence teams to detect risky objects and threat group logos in multi-media data

Learn more about how Fivecast supports traditional intelligence practices to protect forces:
Recent global events and geopolitical tensions have disrupted global supply chains and brought to light additional risks. Organizations must be able to conduct effective, efficient and ongoing due diligence and risk assessment on all parts of their supply chain.
Fivecast can be deployed to rapidly monitor, identify and assess threats to the safety and security of their personnel, facilities, intellectual property, and company reputation. Fivecast can be deployed across the entire supply chain with advanced OSINT capabilities including:
- Advanced data collection and network analysis to identify critical connections and risks
- A customizable risk detection framework to analyze text, images and videos to build a rich picture of supply chain risks
- Multi-lingual and AI-expanded term detection configurable to detect specific risks such as supplier and subsidiary names, facility locations, etc. across over 100 languages
Globalization & the softening of borders along with global conflict has supported the expansion of criminal enterprises across borders. Internet-based communications now mean these groups are able to add virtual borders and barriers that limit access to information, rendering attempts to resolve investigations by traditional means near impossible.
Fivecast is particularly suited to the challenges of identifying and monitoring risks associated with transnational organized crime, providing intelligence teams with:
- Wide geographical breadth of data collection
- Multi-lingual data collection & analysis: 100+ languages
- Graphical network analysis diagrams to link POI’s from masses of unrelated data
- User-trainable risk detectors to uncover variations of logos, images, or posts that may be present in different countries

Learn more about how Fivecast can be deployed for transnational organized crime investigations:
The reality is that there is more information available to fraud detection teams now than ever before, which means that finding the right information, verifying it, seeing the signals in that ‘noise’, and making assessments from them is more challenging than it’s ever been.
Fivecast helps fraud investigation teams in law enforcement, financial intelligence and corporate security with:
- Integrated discovery via people search engines to discover online accounts relevant to investigations quickly
- Correlation of data points across the Surface, Deep, and Dark Web to identify important links between organized crime and legitimate banking institutions
- AI & ML enabled multi-lingual expanded term and concept detection to rapidly identify fraud indicators such as unexplained wealth in multimedia.
The current state of societal and geopolitical tension combined with the proliferation and diversity of online platforms leveraged by threat actors makes open-source intelligence essential to protective security missions. Use cases relative to protective security range from asset and facility protection, event monitoring to workplace protection and more.
Fivecast helps Government agencies and Corporate organizations deploy advanced open-source intelligence capabilities to ensure protective security including:
- Customizable, AI-powered risk detectors to pro-actively identify threats related to current events
- Ongoing and automated data collection to monitor the changing risk picture relative to violent protests or POIs
- Correlation of OSINT data with other intelligence data to develop rich and broad intelligence insights

Learn more about how Fivecast can be deployed to support protective security missions:
Financial institutions and regulated entities must ensure compliance with constantly evolving and complex regulations surrounding Continuous Evaluation (CE) requirements for; Anti-money Laundering (AML), Know Your Customer (KYC) and Combatting the Financing of Terrorism (CFT/CTF).
To meet these requirements, modern enterprise risk management frameworks (RMFs) must be implemented. OSINT can play a pivotal role in strengthening RMFs, both in the CE and onboarding phases. Fivecast automates the data collection and analytics processes, enabling analysts to conduct investigations securely across masses of data that could otherwise overwhelm them:
- Persons of Interest (POI) search performs automated discovery of online account handles from limited information
- Entity-centric data collection with pre-defined detectors targets information of most relevance to an investigation
- Relationships between entities are automatically detected and assessed, including the strength of association






